Description
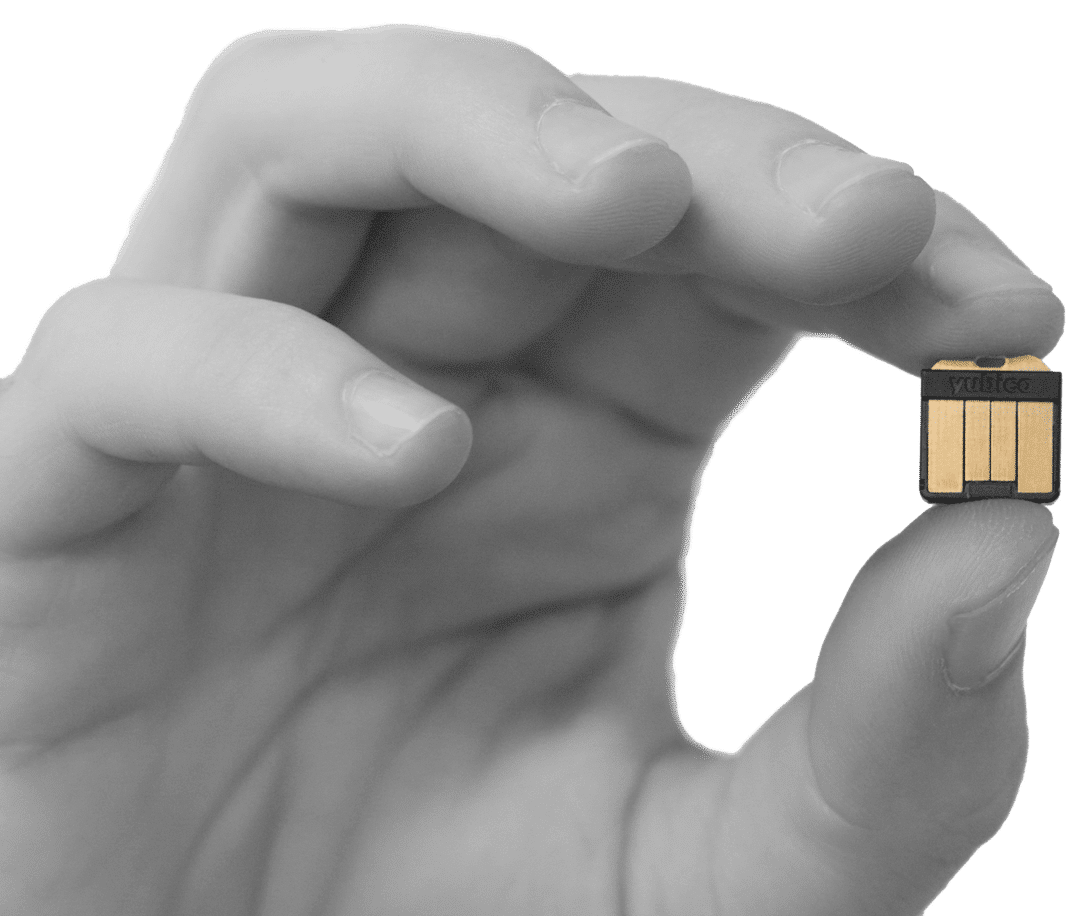
YubiHSM 2 is a hardware module that provides excellent protection against phishing and malware attacks for the root keys of certificate authorities on servers. Being economical and affordable, it can be easily implemented in any enterprise. This module provides a high level of security for organizations working with the Microsoft Active Directory certification service, providing a confident approach to the generation, storage and distribution of digital keys. Its ergonomic “nano” form factor fuully fits inside the USB port, which eliminates the need for additional, bulky equipment, and allows you to flexibly transfer and backup keys offline.
YubiHSM 2 features are available through Yubico’s Key Storage Provider (KSP), for PKCS # 11 industry standard, or Microsoft CNG, or through native support in Windows, Linux, and macOS libraries.
YubiHSM 2 can be used as a comprehensive toolkit for a wide range of open source and commercial applications. The most widely used for hardware generation and verification of digital signatures.
Usage
Adds strong cryptography support
YubiHSM 2 offers robust methods of digital keys generation, storage and delivery. Key protection is performed in secure equipment based on a chip, separately from operations conducted on the server. Mostly used to protect root keys of certification authorities. Features of YubiHSM 2 include: generation, recording, signature, decryption, hashing and key packaging.
Conducts Hardware Cryptographic Operations
YubiHSM 2 can be used as a comprehensive toolkit for small operations, combined with a huge set of open and commercial applications, while covering many products and services. Most often used for hardware generation and verification of signatures.
Protects Microsoft Active Directory Certificates
YubiHSM 2 can provide hardware keys for public key infrastructure based on Microsoft products. Implementing YubiHSM 2 in the Microsoft Active Directory Certificate Services protects not only the root keys of certification authorities, but also all the signing and verification services that use them.
- Secure Operations and Key Storage
- Advanced cryptographic capabilities: RSA, ECC, ECDSA (ed25519), SHA-2, AES
- Secure Session between HSM and Application
- Role-based access control for key usage and distribution
- 16 simultaneous connections
- Ability to provide network access
- Remote control
- Unique “Nano” form factor, low power consumption
- Packing keys using a constant weight code (M of N), res. copy and restore
- Interface based on YubiHSM KSP, PKCS # 11, and native libraries
- Autopsy audit
Capabilities
Secure Operations and Key Storage
Create, import and store keys, then conduct cryptographic operations using HSM equipment to prevent theft of keys during operation or inaction. This provides protection against logical attacks on the server, such as zero-day vulnerability or malware, as well as the consequences of physical theft of the server or its hard disk.
Advanced Cryptographic Features
Advanced Cryptographic Features YubiHSM 2 supports hashing, key packaging, asymmetric signature and decryption, including extended signature, with ed25519. Certification is available for asymmetric base pairs generated on the device.
Secure Session between HSM and Application
A mutually authorized tunnel, with integrity and confidentiality protection, protects the integrity and confidentiality transferred between the HSM and the applications.
Role-based access control for key usage and distribution
All cryptographic keys and other objects within the HSM belong to one or more security domains. Access rights are assigned to each authentication key, at the time of creation, which allows to a certain set of cryptographic or administrative operations to be performed relative to the security domain. Administrators assign rights to the keys based on their intended use, for example, an event monitoring application requires the ability to read the audit log inside the HSM, or the Registration Center needs to sign digital certificates for end users, or the security domain administrator should create or delete cryptographic keys.
16 simultaneous connections
Many applications can establish communication sessions with YubiHSM for cryptographic operations. Sessions can be stopped automatically after inactivity, or extended to improve performance by eliminating the time it takes to create a session.
Ability to provide network access
To increase deployment flexibility, network access to YubiHSM 2 can be provided to applications located on other servers. This can be especially convenient when there are many virtual machines hosted on the same physical server.
Remote control
Easily manage many YubiHSM modules involved remotely, within the whole enterprise – eliminate the difficulties associated with the call of staff and travel costs.
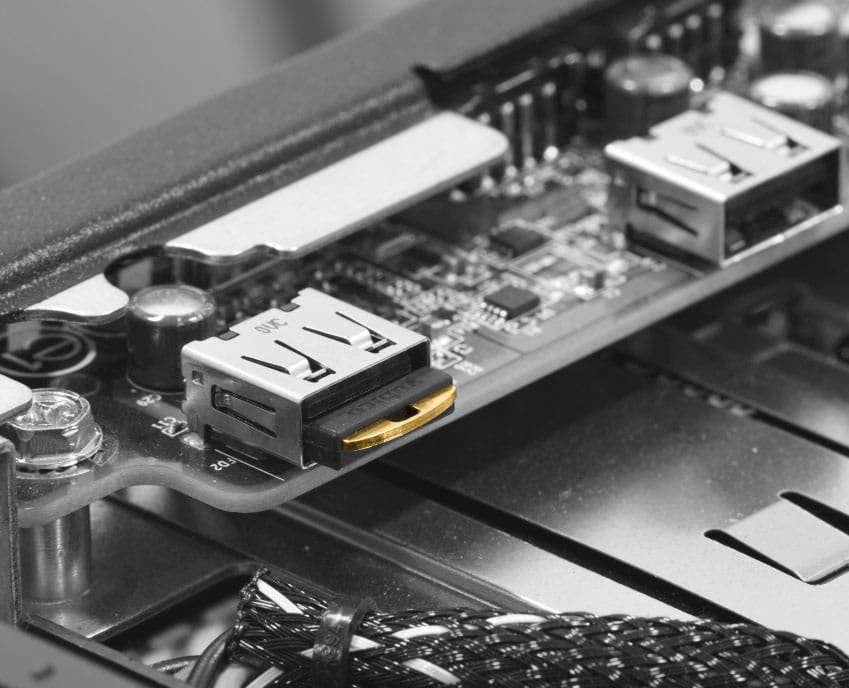
Unique “Nano” form factor, low power consumption
Unique Nano Form Factor, Low Power Consumption The form factor developed by Yubico “Nano” allows the security module to be located completely inside the USB-A port, thus ensuring compactness; without unnecessary details that protrude out the back of the server or front chassis. Consumes a minimum of power – max. 30 mA, which helps save on energy costs.
Packing keys using a constant weight code (M of N), res. copy and restore
Backing up and enabling cryptographic keys on multiple security modules is critical to the enterprise security architecture; it’s risky to provide these opportunities to only one person. YubiHSM supports the installation of M rules from N for the packaging key used to export the keys for further recovery or relocation, so several administrators are required to import and decrypt the key so that it can be used on additional security modules. For example, an enterprise: the Active Directory Certificate Authority private root key can be packaged for 7 administrators (M = 7), and at least 4 of them (N = 4) are required to import and unpack (decrypt) the key on the new security module.
Interface based on YubiHSM KSP, PKCS # 11, and native libraries
Cryptographic applications can control YubiHSM through the Yubico Key Storage Provider (KSP) for Microsoft CNG or industry standard PKCS # 11. Native libraries for direct access to device capabilities are available for Windows, Linux, and macOS.
Autopsy audit
Autopsy audit Inside YubiHSM, a log of all cryptographic and administrative operations that are carried out on the device is stored, and this log can be exported for further monitoring and reporting. Each event (row) in the log is associated with a hash with the previous row and is signed, therefore, this allows the detection of deletion or change of events.
USB support
New feature: YubiHSM 2 can work with the USB hardware layer directly, without the need for an intermediate HTTP mechanism. This feature allows developers to simplify the process of developing solutions for virtualized environments.