YubiHSM 2
Hardware security module enabling cryptographic keys protection for IT solutions
Best cost-effective hardware security module for servers
Secure Cryptographic Keys
The module provides a greater level of security for organizations running Microsoft Active Directory
Rapid integration with hardware-backed security
Integration Faster with Open Source Software with PKCS # 11 Support
Simplified deployment for organizations of all sizes
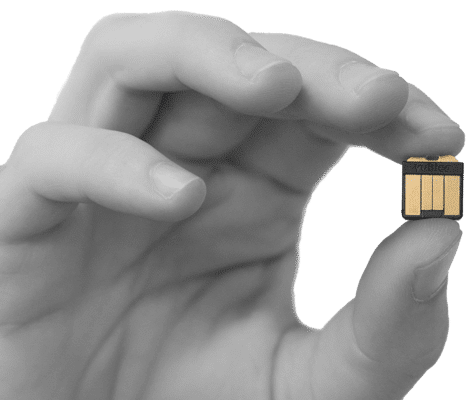
Ultra portable form factor at an affordable price secures a wide range of long-standing and emerging use cases.

Enhanced protection for cryptographic keys
- Prevent poor cryptographic key handling by preventing accidental copying and distribution of cryptographic keys.
- Defend against remote attacks and eliminate remote extraction of private keys by storing cryptographic keys securely on hardware
- Strong hardware-based security ensures highest bar for protection of sensitive information and data.
Rapid integration with hardware-backed security
- Open source SDK enables rapid integration.
- Frees developers to easily build support for hardware-based strong security into a wide array of platforms, applications and services
- Enables organizations to easily make the YubiHSM 2 features accessible through industry standard PKCS#11
YubiHSM 2
YubiHSM 2 provides superior protection of private keys from theft and misuse.
- Cryptographic keys are protected by hardware throughout the life cycle.
- Hardware Security Module (HSM).
- Open source SDK enables rapid integration
- USB – A

Simplified deployment for organizations of all sizes
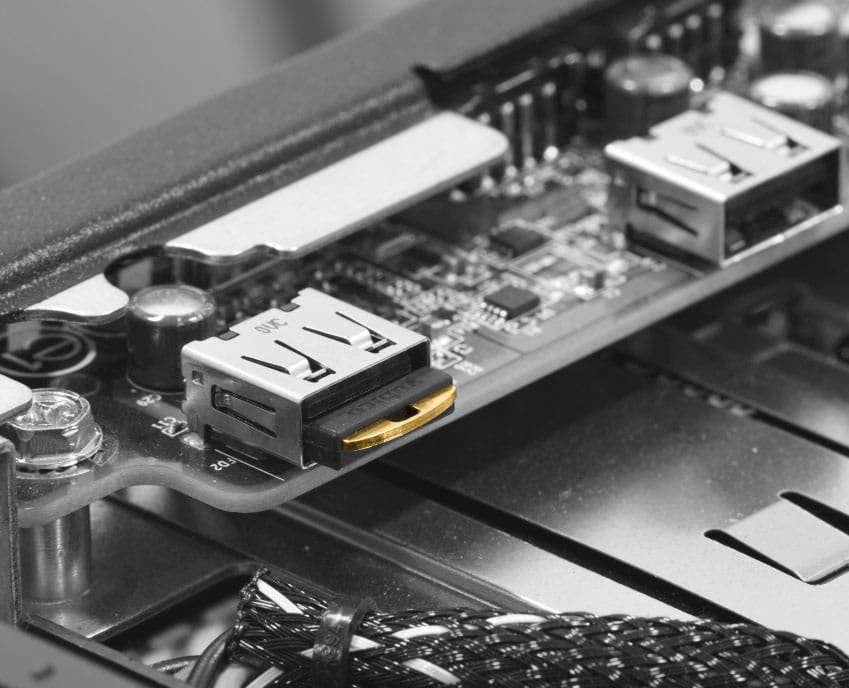
- Ultra-portable and fits easily into a front USB slot on computers and servers
- Secures modern use cases such as cryptocurrency exchanges, IoT gateways and proxies and cloud services
- Secures Microsoft Active Directory certificates

Specifications
Cryptographic Interfaces (APIs)
- Microsoft CNG (KSP)
- PKCS#11 (Windows, Linux, macOS)
- Native YubiHSM Core Libraries (C, python)
Cryptographic capabilities
Hashing (used with HMAC and asymmetric signatures)
- SHA-1, SHA-256, SHA-384, SHA-512
RSA
- 2048, 3072, and 4096-bit keys
- Signing using PKCS # 1v1.5 and PSS
- Decryption using PKCS # 1v1.5 and OAEP
Elliptic curve cryptography (ECC)
- Curves: secp224r1, secp256r1, secp256k1, secp384r1, secp521r, bp256r1, bp384r1, bp512r1, curve25519
- Signing: ECDSA (all exept curve25519), EdDSA ( curve25519 only)
- Decryption: ECDH (all except curve25519)
Key wrap
- Import and export using NIST AES-CCM Wrap at 128, 196, and 256 bits
Random numbers
- On-chip True Random Number Generator (TRNG) used to seed NIST SP 800-90 AES 256 CTR_DRBG
Attestation
- Asymmetric key pairs generated on-device may be attested using a factory certified attestation key and certificate, or using your own key and certificate imported into the HSM
Performance
Performance varies depending on usage Example metrics from an otherwise unoccupied YubiHSM 2:
- RSA-2048-PKCS1-SHA256: ~139ms avg
- RSA-3072-PKCS1-SHA384: ~504ms avg
- RSA-4096-PKCS1-SHA512: ~852ms avg
- ECDSA-P256-SHA256: ~73ms avg
- ECDSA-P384-SHA384: ~120ms avg
- ECDSA-P521-SHA512: ~210ms avg
- EdDSA-25519-32 Byte: ~105ms avg
- EdDSA-25519-64 Byte: ~121ms avg
- EdDSA-25519-128 Byte: ~137ms avg
- EdDSA-25519-256 Byte: ~168ms avg
- EdDSA-25519-512 Byte: ~229ms avg
- EdDSA-25519-1024 Byte: ~353ms avg
- AES-(128|192|256)-CCM-Wrap: ~10ms avg
- HMAC-SHA-(1|256): ~4ms avg
- HMAC-SHA-(384|512): ~243ms avg
Storage capacity
- All data stored as objects. 256 object slots 128KB (base 10) max total
- Stores up to 127 rsa2048, 93 rsa3072, 68 rsa4096 or 255 of any elliptic curve type, assuming only one authentication key is present
- Object types: Authentication keys (used to establish sessions); asymmetric private keys; opaque binary data objects, e.g. x509 certs; wrap keys; HMAC keys
Management
- Mutual authentication and secure channel between applications and HSM
- M of N unwrap key restore via YubiHSM Setup Tool
Software development kit (SDK)
SDK for YubiHSM 2 includes:
- Library YubiHSM Core (libyubihsm) for C, Python
- YubiHSM Shell (command line configuration)
- PKCS#11 module
- YubiKey Key Storage Provider (KSP) for Windows
- YubiHSM Connector
- YubiHSM Setup Tool
- Code Signing Example
Host interface
- (USB) 1.x Full Speed (12Mbit/s) Peripheral with bulk interface
Physical Characteristics
- Form factor: nano designed for confined spaces such as internal USB ports in servers
- Dimensions: 12mm x 13mm x 3.1mm
- Weight: 1g
- Current requirements: 20 mA avg, 30 mA max.
- USB-A
Environmental Compliance
- FCC
- CE
- WEEE
- ROHS
