Application for reliable authentication
Yubico Authenticator

Yubico Authenticator is your extra layer of security
Compatible with YubiKey 5and YubiKey FIPS hardware key series
2FA protection
Generates codes for two-step verification on mobile devices or computers.
Compatibility
Works with iOS, macOS, Windows, Android, and Linux operating systems, supports NFC
Supports YubiKey
Protects accounts in services that are compatible with other authenticators.
Importantly! With Yubico Authenticator, you can use YubiKeys to secure accounts on any service, even those that don’t support security key authentication. It is enough that the service supports any application for 2FA, such as authenticators from Google or Microsoft.

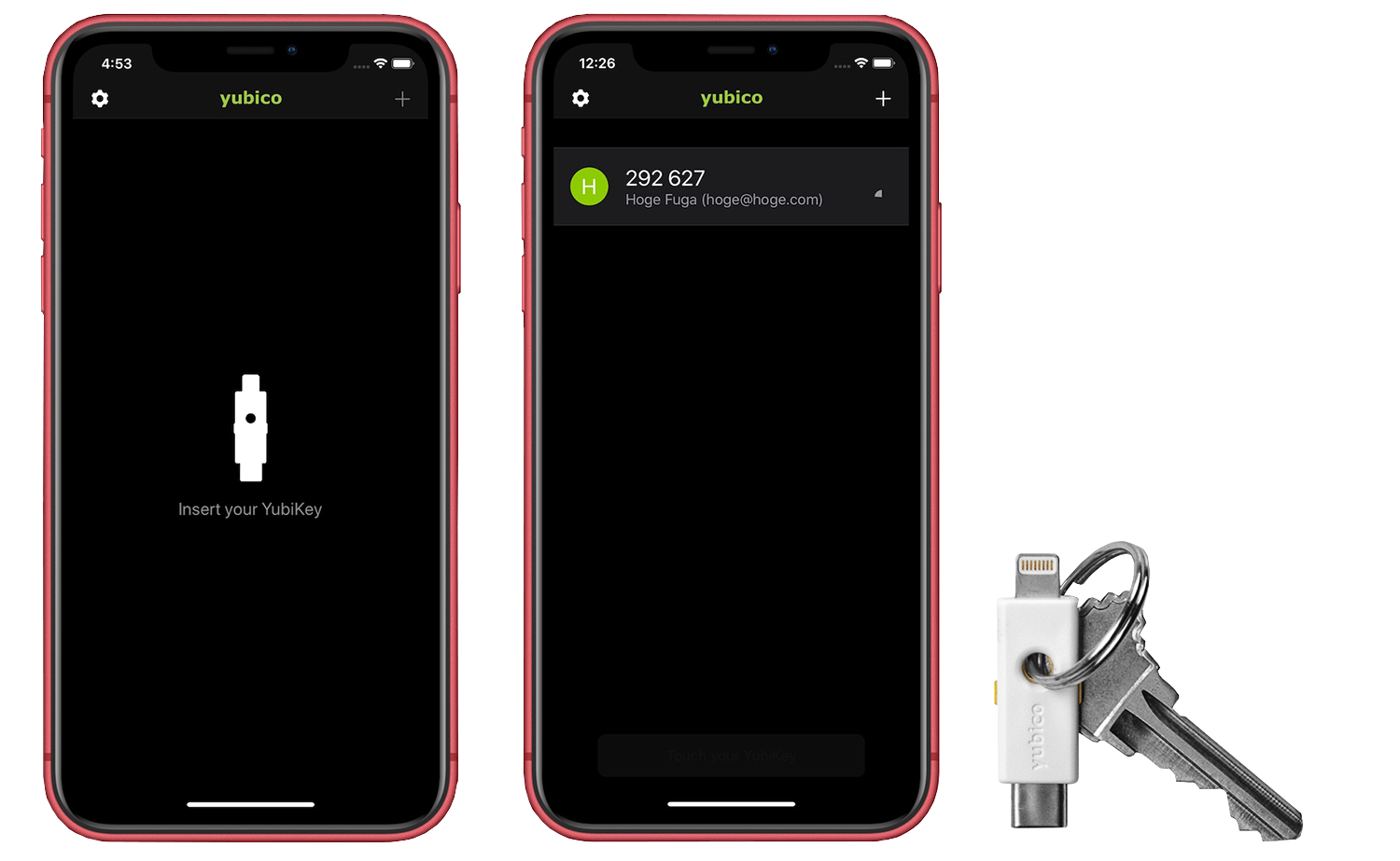
How Yubico Authenticator works
Unlike functionally similar applications, in which it is enough to open the application to receive the code, and the secret key for generating one-time passwords is stored directly in the application’s memory, Yubico Authenticator stores the secret on the physical YubiKey. So to start displaying one-time passwords on the screen, you need to connect the dongle or hold the YubiKey up to the device on which the authenticator is installed. That way, even if your device falls into third-party hands, they won’t be able to read the one-time passwords to your accounts.
We compare authenticators
How Yubico Authenticator works
- The application generates a secret key (in the form of a string or a QR code).
- The authenticator receives the secret key and stores it in the YubiKey’s secret key store (almost impossible to extract).
- The authenticator is unlocked using the YubiKey.
- The authenticator then generates a one-time code based on cryptographic calculations with the secret key and the current time.
How the classic authenticator works
- The application generates a secret key (in the form of a string or a QR code).
- The authenticator receives the key and stores it in the device’s memory (while it can be removed).
- The authenticator generates a one-time code based on cryptographic calculations and taking into account the current time.
This method of additional protection of your password is more reliable, because even if an attacker with the help of spyware can remotely steal information from your device, he will still not be able to log into the account without the YubiKey security key.
Benefits of Yubico Authenticator
The most reliable hardware protection
Easy and simple setup
Protect multiple work and personal records
Access data on different devices
Getting Started with Yubico Authenticator
To get started with Yubico Authenticator, you need to select a version and download it to your device. It’s free.